The software development landscape changes constantly. New areas of specialization, technologies, and methodologies pop into existence every few months, forged by the relentless innovation of the software industry. With it, terms to describe specialized types of developers become part of the unofficial industry lingo and show up in job ads and corporate titles.
Before the existence of the internet, many of these specializations didn’t exist. The worldwide web has shifted most aspects of our lives, including revolutionizing the career paths of software engineers.
There isn’t an official industry glossary of terms. Understanding the skills that each type of developer needs to have is confusing to newcomers, and can be intimidating to non-technical people.
The cheat sheet below highlights the 3 major It Developer categories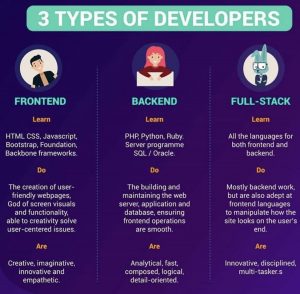
Other tiers similar to frontend, backend and full-stack developer include Middle-Tier Developer, which is a developer who writes non-UI code that runs in a browser and often talking to non-core code running on a server. In general, middle tier is the “plumbing” of a system. The term middle-tier developer is used to describe someone who is not specialized in the front-end or the back-end but can do a bit of both, without being a full stack developer. Only rarely engineers have this as a title, as it is more of a description of a skill set than a career path.